Assess Risk and Strategy
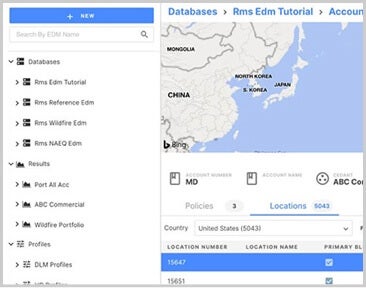
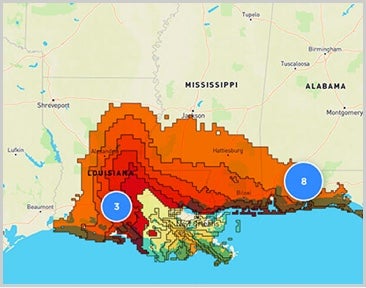
Leverage Moody’s RMS long-standing commitment to deliver market-leading climate risk analytics. We can help our clients to navigate the complex landscape of climate change risks. We can deliver objective, quantitative and actionable risk insights to help client solve climate-related challenges, including:
- Investor and stakeholder communication
- Regulatory reporting and requirements
- Business strategy planning
- Risk management and stress testing